- Prisma Cloud inherits and expands Twistlock's capabilities to offer comprehensive security for cloud-native containers and payloads.
- The platform integrates vulnerability scanning in CI/CD, logs and runtime, prioritizing risks with real-world exploitation context.
- Their CNAPP approach combines CSPM, CWP, CIEM and network security, with native protection for Kubernetes and multicloud environments.
- It offers good performance and scalability, although it requires a learning curve and proper planning of licenses and deployment.
Container security has become a critical issue This is relevant for any company working with Kubernetes, Docker, or microservices architectures in the cloud. The challenge is no longer just deploying faster, but doing so without opening doors to attackers who exploit vulnerable images, weak configurations, or excessive permissions.
Twistlock, now integrated into Palo Alto Networks' Prisma Cloud, It's a leading provider when it comes to seriously protecting containers and cloud-native workloads. The former container security platform has been merged into a comprehensive CNAPP (Cloud Native Application Protection Platform) that covers everything from code to runtime, including CI/CD, logging, runtime, and regulatory compliance.
Microservices architectures and the challenge of securing containers
Microservices architectures are inherently dynamic (and the choice between Docker Compose and Kubernetes)Pods, services, and containers are deployed continuously, versions are updated several times a day, and instances are scaled according to load. This model accelerates development but renders traditional security based on static perimeters and occasional manual reviews obsolete.
Containers ensure that software behaves the same in different environments (dev, pre, production, on-premises, public cloud), and this very portability makes them a very attractive target for attackers. A single vulnerable base image can spread to hundreds or thousands of deployments in a matter of minutes.
Modern container security must cover the entire life cycleFrom image building in the CI/CD pipeline, through register scans, to runtime behavior, any review will always leave dangerous gaps if it's only done before deployment or only during runtime.
Specialized container security tools Prisma Cloud (formerly Twistlock) covers host, network, management stack, build pipeline, image layers, and the containerized application. The goal is to maintain continuous monitoring that adapts to the ephemeral and ever-changing nature of cloud-native environments.
In parallel, the ecosystem has become filled with complementary solutions like Wiz, Snyk, Trivy, Anchore, Aqua Security, Sysdig or Qualys, each with its focus: vulnerability scanning, compliance, runtime defense, CSPM, etc. Prisma Cloud integrates and expands a good part of that type of capability into a single platform.
What are container security tools and why does Prisma Cloud stand out?
Container security tools are software solutions Designed specifically for the security challenges of Docker, Kubernetes, Fargate, ECS, AKS, GKE, OpenShift, and other orchestration platforms. They go beyond image antivirus: they add context, policies, compliance, and visibility across the entire environment.
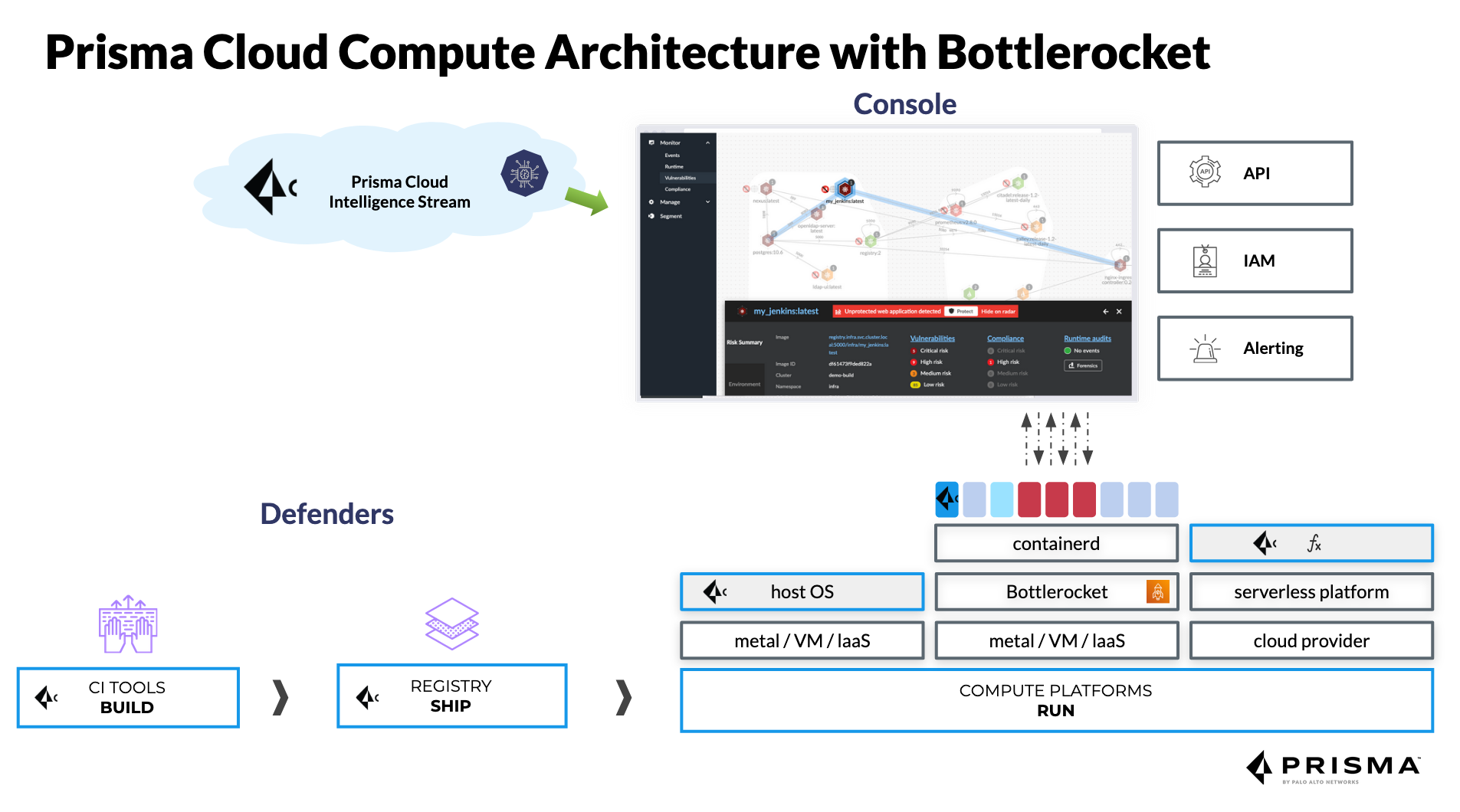
In the case of Prisma Cloud Compute (the direct descendant of Twistlock)We're talking about a platform that protects hosts, containers, serverless functions, and, in general, cloud-native workloads. It offers vulnerability management, compliance controls, runtime defense with rules and machine learning, cloud-native firewalls (such as WaaS for web applications and APIs), and granular access control.
Twistlock was born as a vulnerability management and compliance solution throughout the entire container lifecycle, it focused on scanning images and preventing unsafe components from moving from the development phase to production. Over time, it added continuous monitoring of logs, networks, and runtime, as well as access controls and segmentation.
Following the acquisition by Palo Alto Networks in 2018All these capabilities were incorporated into Prisma Cloud, which already covered other areas of cloud security. The result is a CNAPP capable of managing rules on Docker configurations, images, nodes, plugins, and services, integrating with secret managers like CyberArk or HashiCorp, and consuming Kubernetes audit logs to generate actionable alerts.
This integration allows for very granular visibility of dependencies, packages, image layers and runtime behaviors, both in CI/CD pipelines and in containers running on hosts, container-as-a-service platforms or hybrid and multicloud environments.
Container scanning: a key element in the security strategy
Container scanning is the first line of defense to detect vulnerabilities in base images, third-party libraries, and custom code. Integrating scanning into CI/CD pipelines allows you to catch problems before deployment and avoids having to put out fires in production.
Detecting vulnerabilities early saves time and moneyIt's much cheaper to fix a vulnerable library during the build phase than in a production cluster with dozens of services depending on it. Furthermore, it avoids chaotic rollbacks and unnecessary exposure windows.
Scanning is also vital for protecting the software supply chain.where there are increasingly more external components: public images, third-party packages, artifacts from other equipment, etc. Validating that everything included in the image does not have known CVEs or dangerous configurations is now mandatory.
From a regulatory point of view, many industries require periodic scans of vulnerabilities and evidence that images and containers comply with standards such as GDPR, HIPAA, PCI DSS, or CIS benchmarks. A centralized scanning tool facilitates audits and report generation.
Another advantage is the reduction of the attack surfaceThe scanners detect unnecessary packages, forgotten debugging tools, or components that add no functionality but increase risk. By removing everything superfluous, lighter and much safer images are obtained.
Automation of security in CI/CD and defense against zero-day attacks
Integrate security into CI/CD and practices such as gitops This is what allows us to talk about DevSecOps Seriously. Instead of relying on occasional manual reviews, each commit or build automatically triggers image scans, code analysis, IaC review, and policy checks.
Prisma Cloud Compute integrates with tools such as Jenkins, GitHub, and GitLab. and other CI providers to reject builds that do not comply with the policy, generate reports for developers, and block the promotion of vulnerable artifacts to higher environments.
Automation is also key to mitigating zero-day vulnerabilitiesEven if an image has passed all checks, new CVEs associated with packages included in that image may appear. With continuous scanning of registry entries and running environments, the platform re-evaluates images as soon as the vulnerability database is updated.
This approach minimizes the exposure windowThe organization learns within hours that an image deployed weeks ago has now become problematic, and can prioritize correction based on criticality, internet exposure, data handled, etc.
In terms of reputation, demonstrate regular and automated scans It builds trust with customers, partners, and regulators. Companies that take container security seriously typically stand out clearly in tenders and due diligence processes.

Prisma Cloud Compute (Twistlock): architecture, requirements and deployment
Prisma Cloud is offered in two major deployment flavors: the Enterprise SaaS edition, hosted and managed by Palo Alto Networks, and the self-hosted Compute edition, which the customer deploys on their own infrastructure (on-premises, cloud or hybrid).
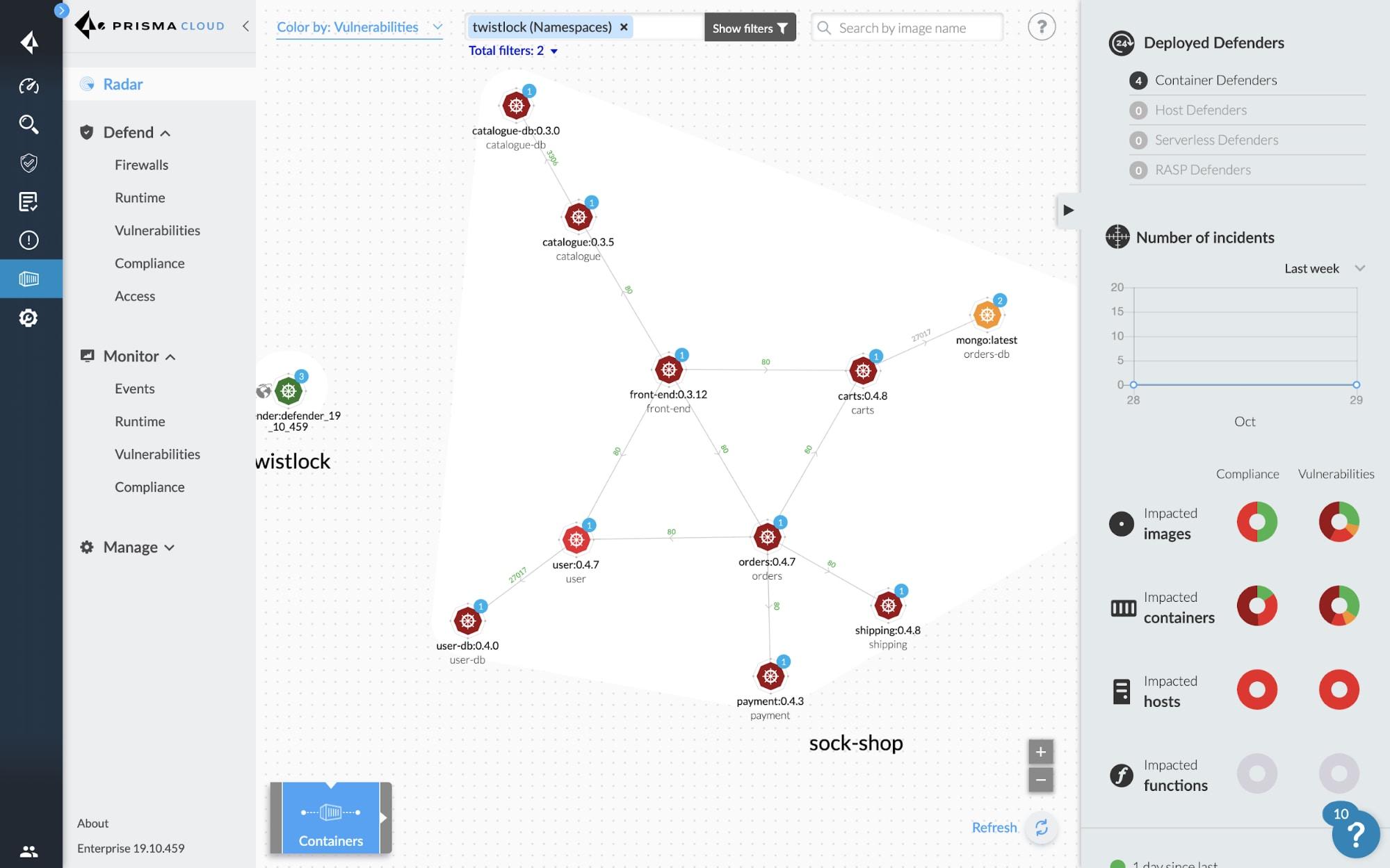
The Compute Edition directly inherits the Twistlock architecturewith a central console that orchestrates policies, collects data and displays global visibility, and Defender agents deployed on hosts, Kubernetes nodes, Fargate, EC2, Windows containers and serverless environments.
Regarding the console's technical requirementsFor small environments (fewer than 1000 Defenders and without intensive log scanning), you can start with about 2 GB of RAM and 2 vCPUs. In large deployments with more than 20,000 Defenders, Palo Alto recommends up to 16 vCPUs, around 50 GB of RAM, and approximately 500 GB of persistent SSD storage.
The Defenders have fairly limited fuel consumption.They can operate with approximately 256 MB of RAM in basic scenarios and scale up to about 2 GB of RAM and 2 vCPUs when performing log scanning or more intensive workloads. In terms of disk space, they require about 8 GB per host, increasing to 20 GB if local log analysis is performed.
If scans are integrated into CIThe recommended space is to have at least 1,5 times the size of the largest image to be scanned per executor, in order to be able to download, analyze and generate the necessary artifacts without bottlenecks.
Prisma Cloud performance and large-scale testing
Palo Alto has published performance tests of Prisma Cloud in very large environments that simulate real-world workloads. In one of these scenarios, we worked with Kubernetes clusters totaling 20,000 hosts, a console with 16 vCPUs and 50 GB of memory, and Defenders with 2 vCPUs and 8 GB of RAM running on an operating system optimized for containers.
In that environment, 323 images and almost 200,000 containers were analyzed.with an approximate density of 9,6 containers per host. The console consumed around 1474 MiB of RAM and 8% of the CPU, while each Defender used about 83 MiB of RAM and 1% of the CPU, quite reasonable figures for a real-time security system.
Individual container scans take an average of 1 to 5 secondswith an additional 10-15% memory consumption and barely 1% CPU usage during the scan. This makes it feasible to integrate scanning even into demanding pipelines without slowing down the time-to-market for new features.
Beyond CPU and RAM numbers, the real impact is seen in SecOps and DevOpsA TEI (Total Economic Impact) study by Forrester Consulting for Prisma Cloud calculated a return on investment of 264%, an improvement in SecOps efficiency valued in millions of dollars, and a notable reduction in materially serious security incidents.
Another interesting metric is the reduction in incident resolution time.Users report going from analyses that previously took days to investigations that are completed in about 3,3 hours, thanks to unified telemetry and dashboards that centralize logs, alerts and network context, IAM and configuration.

Prisma Cloud security capabilities inherited and expanded from Twistlock
The core of what Twistlock was focused on vulnerability management throughout the entire container lifecycle. Prisma Cloud follows this approach and adds extra layers of context and automation to prioritize what to fix first.
The platform establishes a risk prioritization based on known CVEsSeverity, exploitability, actual runtime exposure, service criticality, and the existence of remediation paths are all considered. It offers remediation guides, layered image analysis, and Top 10 lists of the most critical vulnerabilities for each service.
At the active protection level, Prisma Cloud controls severities of alerts and blocks, allowing you to adjust for each service and group which behaviors should only generate warnings and which should be blocked during build or at runtime, for example in response to attempts to execute dangerous commands within a container.
The accuracy of vulnerability detection is enhanced with more than 30 upstream sources which feed the CVEs and alerts database. This reduces false positives and helps teams focus on what really matters, instead of wasting time triaging noise.
Furthermore, Prisma Cloud integrates vulnerability management across the board.It scans code repositories, container logs, CI/CD pipelines, and runtime environments. This avoids the classic problem of having isolated tools that don't communicate with each other.
Prisma Cloud as CNAPP: beyond container security
Currently, Prisma Cloud is a complete CNAPP platform which goes far beyond Twistlock. It includes modules for cloud security posture management (CSPM), workload protection (CWP), rights management (CIEM), network security, data security, and controls over infrastructure as code and CI/CD pipelines.
In CSPM, the solution reviews configurations in AWS, Azure, GCP, OCI and Alibaba CloudDetecting excessive permissions, exposed resources, misconfigured services, and deviations from frameworks such as CIS, PCI, or internal company benchmarks. Correction can be manual or automated.
In the CWP environment, Prisma Cloud protects hosts, containers, and serverless functions. with vulnerability management, process monitoring, network defense, file integrity control, and behavioral rules that can be based on signatures, dynamic analysis, and machine learning.
The CIEM module focuses on cloud rights and identitiesIdentifying credentials with excessive privileges, unused roles, exposed keys, or cross-account access that can lead to dangerous lateral movements after an initial breach.
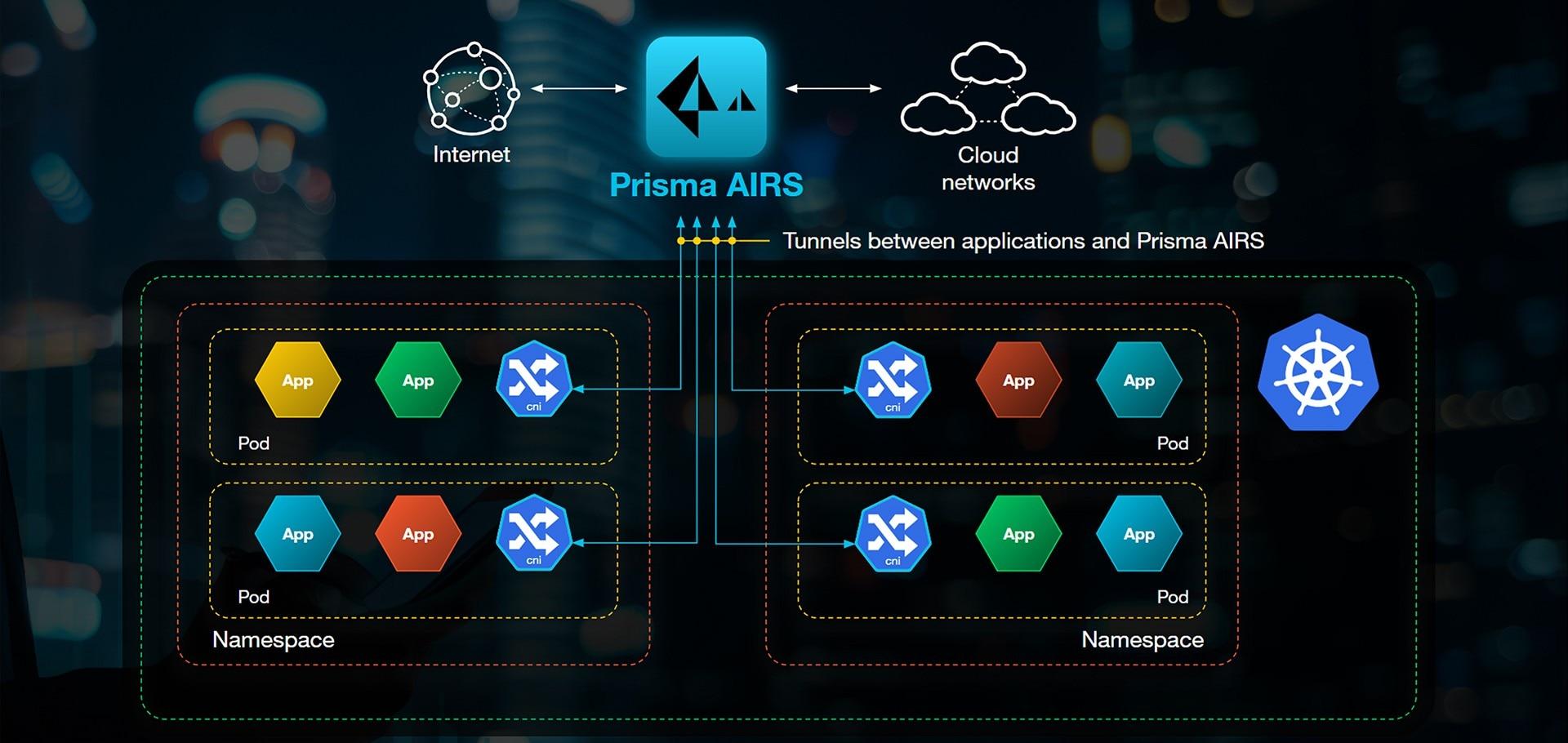
The network security component includes anomaly detection capabilities, attack path analysis, tag-based segmentation and integration with next-generation Palo Alto firewalls (PAN-OS, Strata Cloud Manager, Panorama), enabling consistent policies between the traditional network world and Kubernetes.
Native security for Kubernetes and containers with Prisma Cloud
One of Prisma Cloud's strengths is its native Kubernetes protectionIt integrates with the control plane to provide direct visibility of containers, pods, and namespaces, and applies dynamic policies based on labels instead of rigid IP addresses.
The solution can be coordinated with standard kubectl, CNI chaining, and Helm chart annotations. to propagate security metadata with each deployment. This makes it easier for network, runtime, and compliance rules to be automatically applied based on context (environment, equipment, criticality, internet exposure, etc.).
Prisma Cloud can also ingest Kubernetes audit logs to detect suspicious events, unexpected changes in roles, creation of service accounts with dangerous privileges, or modifications to sensitive objects. All this information is converted into alerts and dashboards in a single console.
Regarding WAAS (Web Application and API Security)The module protects web applications and APIs running on Kubernetes or containers against typical OWASP Top 10 attacks (injection, XSS, broken access control, etc.), as well as more advanced exploitation attempts. It can operate in alert-only mode or active blocking mode.
Combining these capabilities with Palo Alto firewallsOrganizations can unify visibility and control from the network level to the application load, using the same sources of truth for centralized identities, labels, and policies.
Security status, vulnerabilities and compliance at Prisma Cloud
Like any complex software, Prisma Cloud has had vulnerabilities. Palo Alto Networks has been proactively addressing these vulnerabilities. Past examples include local privilege escalation, cross-site scripting (XSS) in the web console, and incorrect cryptographic checks, with CVEs such as CVE-2021-3042 and CVE-2021-3033 receiving high CVSS scores.
The company maintains an active vulnerability response programeven assigning its own identifiers (PRISMA) when a public CVE does not yet exist. Patches are distributed quickly, especially in the SaaS edition, which is continuously updated without customer intervention.
At the level of encryption and data protectionPrisma Cloud stores log and telemetry metadata in encrypted services such as RDS or Redshift managed in the cloud, complying with best practices for data security in transit and at rest.
Regarding authentication, robust methods such as SAML are supported. to integrate Compute Edition with corporate identity providers, facilitating SSO and applying MFA policies or centralized session management.
The platform also helps organizations meet compliance standards By offering predefined checks, exportable reports, dashboards by regulation, and the ability to create custom controls, this is essential in sectors such as finance, healthcare, and public administration.
Technical requirements, support and compatibility
Prisma Cloud's licensing model is based on credits. Customers consume based on the modules and workloads they want to protect (Enterprise Edition, Compute Edition, etc.). This allows the cost to be tailored to the reality of each organization, although it also adds some complexity when sizing and budgeting.
Operating system compatibility is broadThe self-hosted Compute console runs on x86_64 Linux distributions, while Defenders supports a wide variety of Linux hosts on x86_64 and ARM64, Windows containers, and common versions of Docker Engine and container runtimes.
In terms of public clouds, Prisma Cloud covers AWS, Azure, and GCP.In addition to providers like Oracle Cloud Infrastructure or Alibaba Cloud, it's designed for multicloud and hybrid environments, with deep APIs for integration with pipelines, external security tools, and DevOps ecosystems.
The SaaS edition is continuously updatedTherefore, the classic concept of "end of support" does not apply in the same way. In the self-hosted Compute Edition, there are version lifecycles, aligned with Palo Alto's product policies, which teams must keep in mind when planning upgrades.
Regarding support, user opinions are somewhat mixed.Many positively value the breadth of documentation and technical capabilities, while others mention that the support experience can be inconsistent, with response times that could be improved in some cases.
Market vision, alternatives and user perception
Within the CNAPP and container security framework, Prisma Cloud competes with players like Wiz, Orca Security, Aqua Security, Sysdig, Microsoft Defender for Cloud, Lacework, Check Point CloudGuard, Trend Micro Cloud One, Qualys, SentinelOne Singularity Cloud Security or SCA/DevSecOps solutions like Checkmarx One and Veracode.
Prisma Cloud's main advantage is its wide coverage area.From IaC and CI/CD to runtime security, including CSPM, CWP, CIEM, network security, and data security, consolidating everything onto a single platform is often a very compelling argument for organizations looking to reduce the number of tools and dashboards.
Among the strengths most cited by users Highlights include unified visibility of cloud assets, the ability to automate fixes, the power of its query languages (RQL/KQL) for investigating incidents, and good integration with cloud providers and third-party technologies.
Among the weaknesses, the learning curve is mentioned above all. (It's not a trivial tool) and there's a feeling that some features are still developing. Some also find the licensing model somewhat convoluted and point out that the support experience could be more consistent.
Even with those drawbacks, Prisma Cloud is perceived as a strong solution For companies with complex infrastructures, especially those already working with Palo Alto Networks in other security layers and wanting to align policies across network, endpoints, and cloud workloads.
The evolution of Twistlock within Prisma Cloud This has resulted in a very complete platform for protecting containers and cloud-native applications: it controls vulnerabilities from the code, automates CI/CD scans, monitors logs and runtime, integrates natively with Kubernetes and public clouds, and above all adds a layer of context and prioritization that helps teams focus on what is truly critical without being overwhelmed by alerts.
Table of Contents
- Microservices architectures and the challenge of securing containers
- What are container security tools and why does Prisma Cloud stand out?
- Container scanning: a key element in the security strategy
- Automation of security in CI/CD and defense against zero-day attacks
- Prisma Cloud Compute (Twistlock): architecture, requirements and deployment
- Prisma Cloud performance and large-scale testing
- Prisma Cloud security capabilities inherited and expanded from Twistlock
- Prisma Cloud as CNAPP: beyond container security
- Native security for Kubernetes and containers with Prisma Cloud
- Security status, vulnerabilities and compliance at Prisma Cloud
- Technical requirements, support and compatibility
- Market vision, alternatives and user perception
